Nearly four years after introducing Lockdown Mode, Apple says the security feature has an impressive track record: the company has not seen a single successful spyware attack against an iPhone with Lockdown Mode enabled.
According to an Apple spokesperson speaking to TechCrunch, the company is “not aware of any successful mercenary spyware attacks against a Lockdown Mode-enabled Apple device.”
That’s a strong claim considering how aggressively governments and private spyware firms continue to target smartphones.
What Lockdown Mode actually protects against
Apple introduced Lockdown Mode in 2022 as an optional security setting designed to protect users from highly targeted attacks, particularly those involving government-grade spyware.
These attacks are often carried out using tools developed by companies like:
- NSO Group
- Intellexa
- Paragon Solutions
Such spyware platforms have historically targeted journalists, activists, political figures, and corporate executives.
Lockdown Mode works by aggressively limiting system functionality to reduce potential attack paths.
Security researchers say the same thing
Independent investigators have also not found evidence of Lockdown Mode being bypassed.
Researchers from organizations such as:
- Amnesty International
- Citizen Lab
have documented numerous spyware attacks targeting iPhones.
However, in those investigations none involved a device that had Lockdown Mode enabled during the attack.
In fact, researchers have seen Lockdown Mode actively block spyware attempts.
Citizen Lab previously observed the feature preventing attacks using Pegasus spyware developed by NSO Group, as well as Predator spyware tied to Intellexa.
SUGGESTED: iPhone 17’s Hidden Upgrade: New Memory Security Feature Explained
Why Lockdown Mode is so difficult to bypass
Security experts say Lockdown Mode dramatically reduces the ways attackers can reach an iPhone.
According to Apple security researcher Patrick Wardle, the feature works by shrinking the attack surface of the device.
In practice, this means:
- Message attachments are heavily restricted
- Certain web technologies used by exploits are disabled
- Many zero-click attack techniques become impossible
This forces attackers to rely on more complex and expensive exploit chains, which drastically raises the difficulty of compromise.
In some cases, spyware has even been seen aborting attacks entirely when Lockdown Mode is detected.
Apple has sent spyware warnings to users worldwide
Over the past several years, Apple has notified users in more than 150 countries when their devices were believed to be targeted by spyware.
The company has never disclosed exactly how many notifications it has sent, but security researchers believe the number likely ranges from dozens to potentially hundreds of users.
These alerts show that Apple has increasing visibility into spyware activity across its ecosystem.
Lockdown Mode remains Apple’s most aggressive security feature
Even critics of Apple’s security model acknowledge the significance of Lockdown Mode.
By disabling many common exploitation techniques, the feature effectively eliminates entire classes of attack vectors used by spyware developers.
For everyday users the restrictions can feel limiting, but for people at risk of targeted surveillance, the trade-off can be worth it.
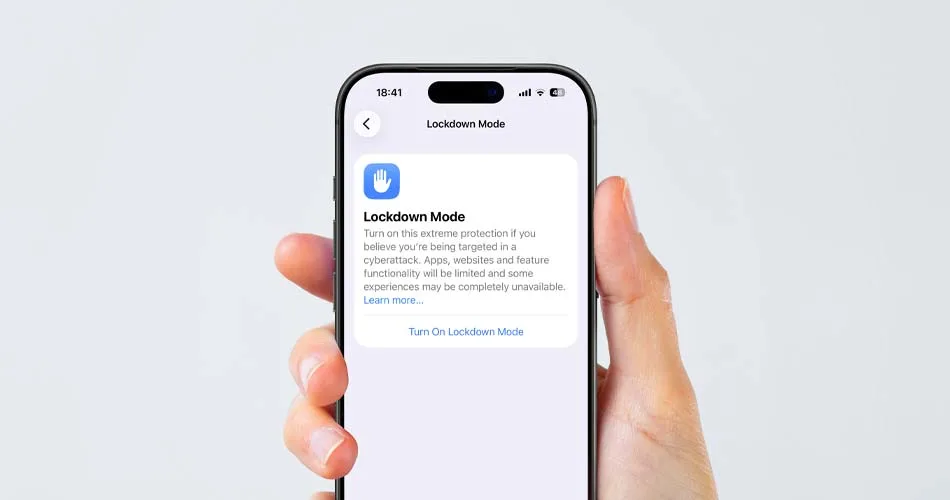
How to enable Lockdown Mode
If you want to turn on Lockdown Mode, we already published a detailed guide explaining how it works and how to enable it on your device. Read here: Lockdown Mode Blocked the FBI. Here’s How to Use It on Your iPhone.
That guide also explains how Lockdown Mode previously helped block an investigation attempt involving the FBI.






